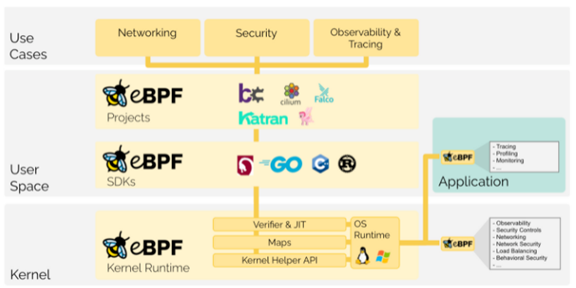
What is eBPF, and why is it so important?
The Extended Berkeley Packet Filter (eBPF) functions constitute a relatively new and powerful set of capabilities embedded in the Linux kernel. First released in 2014 (w/ Linux 3.18) we are seeing accelerating adoption of eBPF for very good reason.
The access that eBPF provides enables a variety of important use-cases in modern cloud-native environments. Use-cases span across application and network performance monitoring, service mesh, load balancing, continuous discovery, dynamic topology and anomaly detection for a variety of development, systems engineering, operations, cloud infrastructure, 5G / IoT, and cybersecurity applications. We discuss these in more detail further below.
Read More
Tags:
network engineering,
network preformance,
Real-Time Monitoring,
mantis,
containers,
5G
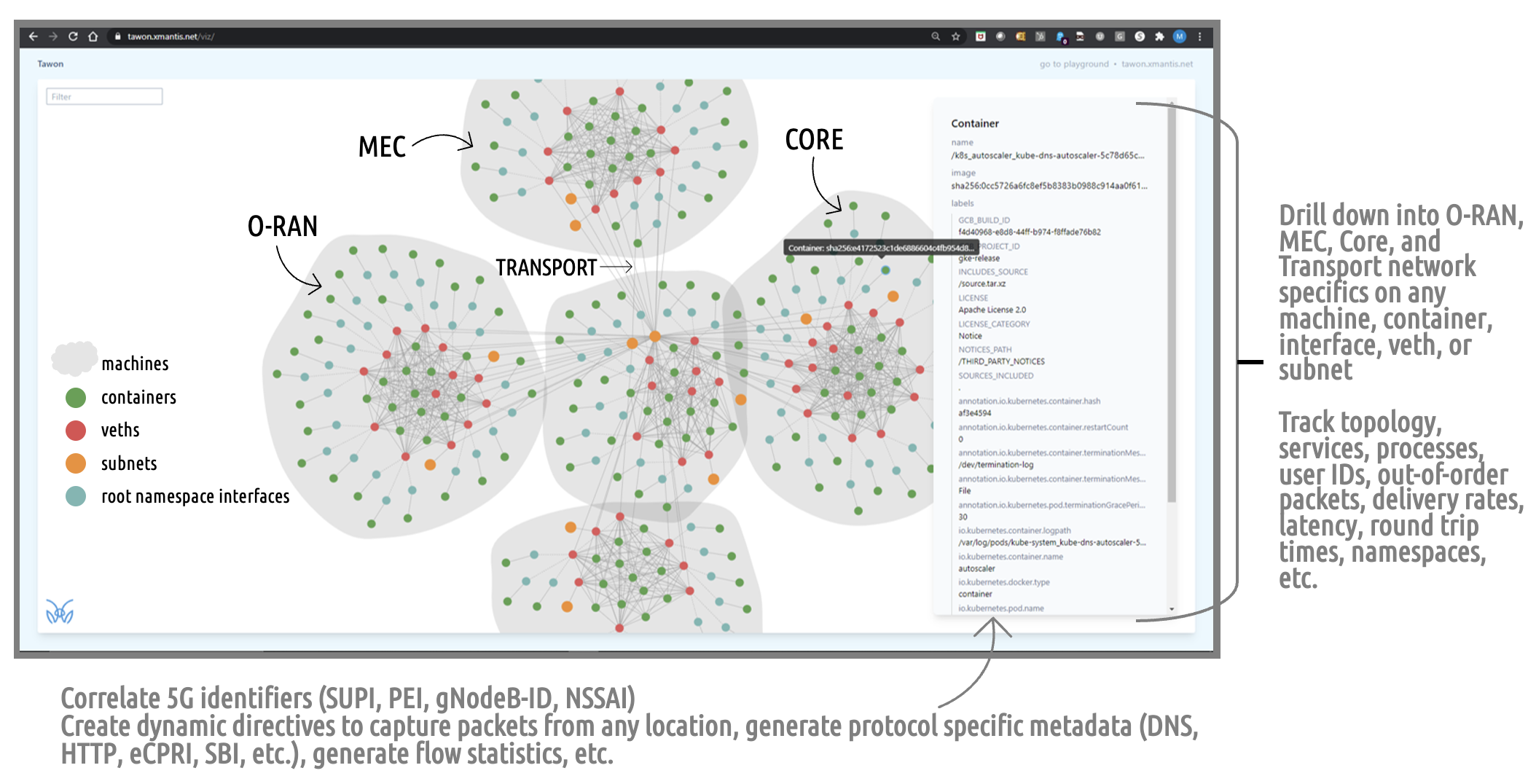
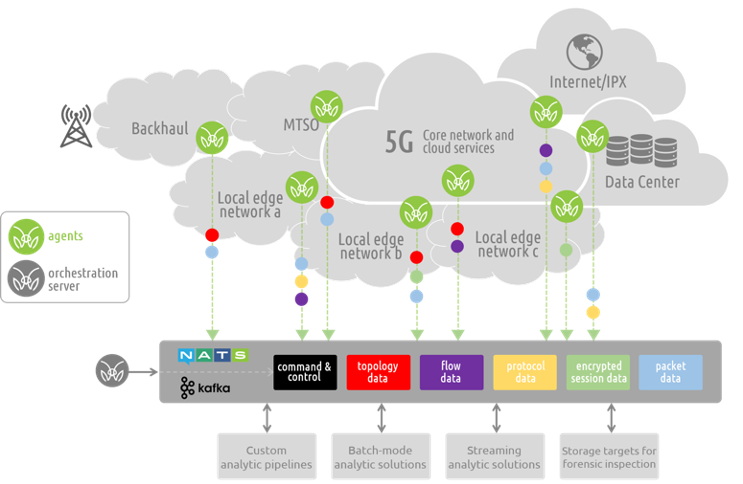
How to Get Visibility into 5G SA Ephemeral and Cloud-native Network Resources
Cloud native and containerized architectures are becoming the de facto design standard for 5G networks and applications. In the telecommunications industry, the players are focused on building out 5G Stand Alone (SA) deployments to deliver the promise of faster connection speeds to enable IoT, medical, autonomous use cases - not to mention improved communications, support the streaming of real-time content and the promise of a myriad of new applications and services. As we work with Tier 1 operators, MVNOs and analytics providers we are encountering a staggering issue: they can no longer adequately monitor, correlate, and measure critical network and application communications events at the container level and across the infrastructure.
Read More
Tags:
Real-Time Monitoring,
mantis,
cybersecurity,
cloud native network function,
5G
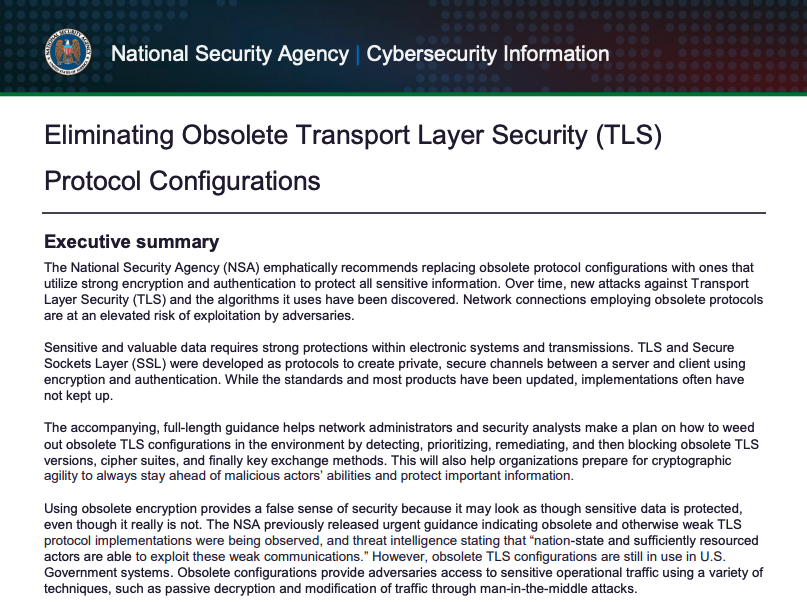
The recently announced NSA "instructions for National Security System (NSS), Department of Defense (DoD) and Defense Industrial Base (DIB) system administrators on how to detect, prioritize and replace unauthorized or deprecated TLS protocols with ones that meet current standards.”
Encrypting communications is one of the most critical tools for protecting data. However, if older and out-of-date encryption protocols are in use, that presents a vulnerability that could be exploited to gain access to systems or networks. Updating to the latest TLS 1.3 and the heavily supported TLS 1.2 along with compliant cipher suites and strong authentication is recommended.
Read More
Tags:
cyber security,
Real-Time Monitoring,
mantis,
cybersecurity
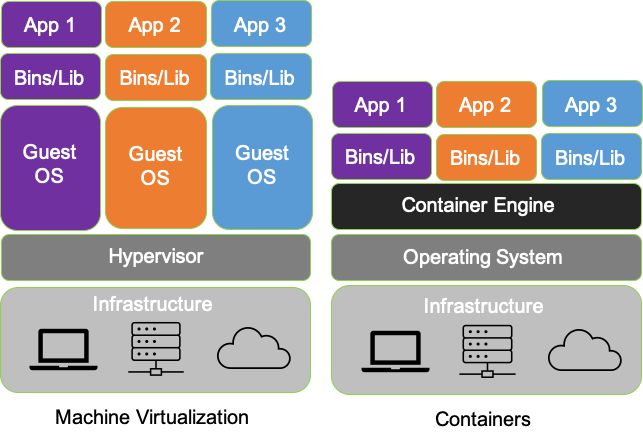
In our last post “Introducing the MantisNet CVF: Solving Cloud Native, Serverless, Observability Challenges“ we provided an overview of the Containerized Visibility Fabric (CVF) capabilities and made some assertions about how revolutionary and disruptive cloud-native technologies are, the resulting opacity problems, as well the art of the possible insofar as enabling next-generation observability.
In this installment we’ll go into more detail as to what exactly we mean by cloud-native observability as well as the significance, deeper implications of it, interoperability and investment protection. So, let’s revisit containerization, and by extension, why cloud-native observability is so revolutionary.
Read More
Tags:
Real-Time Monitoring,
Data-In-Motion,
mantis,
cybersecurity,
containers,
cloud native network function
Solving the opacity problem - Bringing clarity to traffic obscured by encryption.
There are many reasons that the use of encryption will continue to increase as it provides a method of privacy and security of communications and lowers the risk of information loss. However, encrypted session traffic does pose a challenge in achieving visibility and observability of network events for day-to-day operational management, risk detection and response, and lawful intercept scenarios.
How can teams better leverage the information contained in encrypted network traffic sessions for real-time network visibility?
Read More
Tags:
Real-Time Monitoring,
Data-In-Motion,
mantis,
cybersecurity,
containers
The MantisNet Containerized Visibility Fabric (CVF) is now generally available, and we want to provide a deeper dive into the challenges that we’ve seen with network visibility which compelled us to develop this much needed cloud native observability solution.
As we will discuss more deeply in this and future posts; serverless, cloud native systems are unique in that applications are deployed as microservices and containerized applications which can both more fully exploit the capabilities of the underlying machines and are further decoupled from the constraints of hypervisors. This provides programmatic visibility and access to the underlying nodes (hardware - machines) in such a way as to enable better scaling, fault isolation, observability and control.
In the cloud native world; network topology (physical and virtual) is hidden, interfaces (network namespaces) are hidden, data flows are hidden, and to make matters even more challenging - resources are dynamically configured, provisioned, deployed and reused.
Read More
Tags:
Real-Time Monitoring,
mantis,
containers,
cloud native network function
5G network architectures are redefining how resources are deployed, managed and utilized within a communications network. A fair blanket statement regarding these changes is that 5G is taking full advantage of cloud-native and virtualization technologies - even pushing them to the next level. These range from cutting edge, revolutionary 100% cloud native deployments from new entrants such as Rakuten, to the more measured non stand-alone (NSA) and hybrid architectures being deployed by the existing wireless service providers. One thing is clear- the days of capital-intensive dedicated physical infrastructure is meaning less and less as cloud-native technology is used to deploy dynamic, service-oriented, and highly scalable resources to deliver on the promises of 5G.
But, what does this mean for data visibility?
Read More
Tags:
network engineering,
network preformance,
Real-Time Monitoring,
mantis
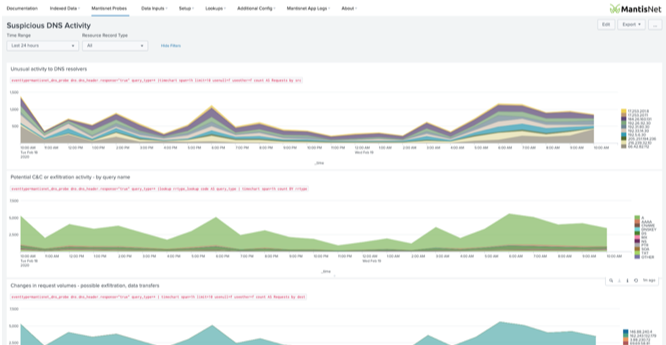
As we’ve shared previously - networks are the circulatory and nervous systems of your enterprise. Indeed; “the network is the computer”, and networks are an invaluable source of ground-truth. From a communications perspective, you can learn a lot by directly observing who is speaking, to whom they are speaking, the language they are using, the tone of voice, and the content of the communications. When it comes to network communications and metadata the analogies are obvious: in the case of DNS traffic- mapping URLs into IP addresses, and identifying underlying services and connected devices - in the case of TLS protocol, getting detailed insights into the encryption capabilities and device characteristics - likewise the GTP protocol provides geo-location specific information, and in the case of the MODBUS protocol, understanding the communications within industrial control systems.
Read More
Tags:
Real-Time Monitoring,
Data-In-Motion,
mantis,
cybersecurity
Announcing the MantisNet Network Stream ProcessorSM App for Splunk
We’re excited and proud to announce that the MantisNet Network Stream ProcessorSM (NSP) App for Splunk is now available.
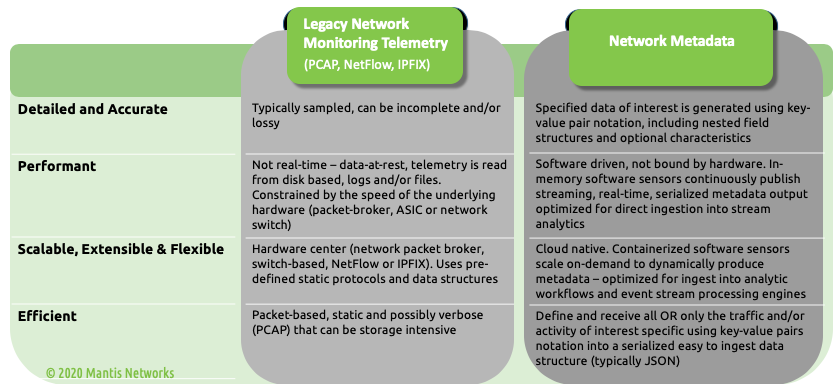
The App enables ingestion of streaming network metadata using key-value pairs: a powerful, new form of serialized metadata produced by MantisNet sensors. Customers can now access, integrate and manage these new forms of lossless, ultra-efficient, ultra-accurate and high-resolution metadata, to support continuous real-time network detection and response in Splunk.
Read More
Tags:
Real-Time Monitoring,
DNS Monitoring,
Data-In-Motion,
mantis,
cybersecurity
This is a continuation of our blog series on the advanced functions for network visibility solutions with fully programmable data pipelines. Read our introduction to the series here.
Another great example of the power behind fully programmable pipelines is the ability to gain insight into the actual visibility solution itself. Solutions such as the MantisNet RFP-NG are able to leverage the processing logic of these pipelines to better visualize what types of events are unfolding on the wire over time and provide metrics related to the rules that are running. Once again, let’s simplify things here for a moment to best understand this concept….
Read More
Tags:
network preformance,
cyber security,
IT operations,
Real-Time Monitoring,
DNS Monitoring,
mantis